Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Palo Alto Networks Exam PCNSA Topic 4 Question 17 Discussion
Actual exam question for
Palo Alto Networks's
PCNSA exam
Question #: 17
Topic #: 4
[All PCNSA Questions]
Topic #: 4
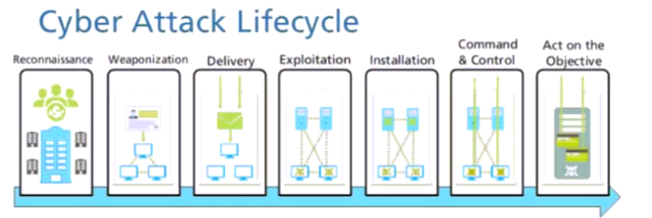
Given the cyber-attack lifecycle diagram identify the stage in which the attacker can run malicious code against a vulnerability in a targeted machine.
Suggested Answer:
A
Currently there are no comments in this discussion, be the first to comment!