Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Microsoft AZ-700 Exam - Topic 13 Question 40 Discussion
Actual exam question for
Microsoft's
AZ-700 exam
Question #: 40
Topic #: 13
[All AZ-700 Questions]
Topic #: 13
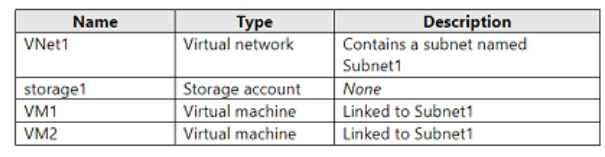
You have an Azure subscription that contains the resources shown in the following table.
You need to ensure that VM1 and VM2 can connect only to storage1. The solution must meet the following requirements:
* Prevent VM1 and VM2 from accessing any other storage accounts.
* Ensure that storage1 is accessible from the internet.
What should you use?
Suggested Answer:
D
Joseph
4 months agoNorah
5 months agoBulah
5 months agoGerald
5 months agoAvery
5 months agoAndra
5 months agoAdaline
5 months agoBrandon
5 months agoKenneth
5 months agoCelia
6 months agoAdela
6 months agoBrittani
6 months agoJoanna
6 months agoEleonore
6 months agoEliseo
6 months ago