New Year Sale 2026! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Linux Foundation CKAD Exam - Topic 3 Question 29 Discussion
Actual exam question for
Linux Foundation's
CKAD exam
Question #: 29
Topic #: 3
[All CKAD Questions]
Topic #: 3
Refer to Exhibit.
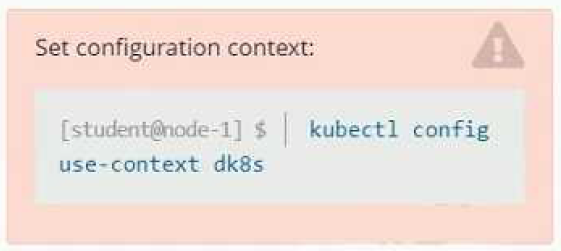
Set Configuration Context:
[student@node-1] $ | kubectl
Config use-context k8s
Context
A user has reported an aopticauon is unteachable due to a failing livenessProbe .
Task
Perform the following tasks:
* Find the broken pod and store its name and namespace to /opt/KDOB00401/broken.txt in the format:

The output file has already been created
* Store the associated error events to a file /opt/KDOB00401/error.txt, The output file has already been created. You will need to use the -o wide output specifier with your command
* Fix the issue.

Suggested Answer:
A
Chantell
3 months agoJeffrey
4 months agoVirgilio
4 months agoWhitley
4 months agoCecilia
4 months agoRolande
5 months agoNicolette
5 months agoPaola
5 months agoCarrol
5 months agoAlishia
5 months agoEffie
5 months agoEileen
5 months agoAmber
5 months agoLeontine
5 months agoTamesha
5 months agoDelsie
5 months agoSheldon
5 months agoArlette
5 months agoDerrick
1 year agodavid bbaker
1 year ago