HPE7-A02 Exam Questions
- HP Aruba Certifications
- HP Aruba Certified Network Security Professional ACNSP Certifications
- Topic 1: Define Security Terminology: This section of the exam measures the skills of Security Analysts and covers essential security concepts and terms. It includes understanding key definitions and their applications in network security. A skill to be measured is the ability to define critical security terms accurately.
- Topic 2: Describe PKI Dependencies: This section assesses the skills of Network Security Engineers and focuses on Public Key Infrastructure (PKI) dependencies. It addresses how PKI supports secure communication and authentication processes in a network environment. A key skill measured is understanding the role of certificates in securing communications.
- Topic 3: Mitigate Threats Using CPDI: This section evaluates the skills of Network Administrators and emphasizes using ClearPass Device Insight (CPDI) to identify traffic flows and apply tags. It also covers using ClearPass Policy Manager (CPPM) to take actions based on those tags. A significant skill measured is the ability to implement traffic tagging effectively.
- Topic 4: Explain the Methods and Benefits of Profiling: This section measures the skills of Security Engineers and focuses on profiling methods for identifying devices on a network. It discusses various profiling techniques and their benefits for enhancing security posture. A key skill assessed is the ability to analyze device behavior for security insights.
- Topic 5: Explain How Aruba Solutions Apply to Different Security Vectors: This section targets Security Architects and covers how Aruba solutions address various security vectors. It highlights the integration of Aruba products into a comprehensive security framework. A skill measured here is understanding how different solutions work together to enhance network security.
- Topic 6: Explain Zero Trust Security with Aruba Solutions: This section assesses the skills of Cybersecurity Specialists and focuses on implementing Zero Trust Security principles using Aruba solutions. It discusses how these solutions enforce strict access controls based on user identity and device health. A critical skill measured is applying Zero Trust concepts in real-world scenarios.
- Topic 7: Explain WIPS and WIDS, Describe the Aruba 9x00 Series: This section evaluates the skills of Wireless Network Engineers and covers Wireless Intrusion Prevention Systems (WIPS) and Wireless Intrusion Detection Systems (WIDS). It also describes the features of the Aruba 9x00 Series access points. A key skill measured is understanding how WIPS/WIDS enhance wireless security.
- Topic 8: Describe Log Types and Levels: This section measures the skills of IT Auditors and focuses on different log types and levels within network systems. It includes using CPPM's ingress event engine to integrate with third-party logging solutions. A significant skill assessed is interpreting log data for security monitoring.
- Topic 9: Explain Dynamic Segmentation: This section targets Network Architects and covers dynamic segmentation, its benefits, and use cases in network design. It emphasizes how segmentation can enhance security by isolating different network segments. A key skill measured is implementing segmentation strategies effectively.
- Topic 10: Device Hardening: This section assesses the skills of Systems Administrators and focuses on securing network infrastructure through device hardening techniques. It includes advanced authentication methods like TACACS+ authorization and multi-factor authentication. A critical skill measured is applying hardening practices to secure devices.
- Topic 11: Secure WLAN: This section measures the skills of Wireless Security Specialists and emphasizes deploying AAA (Authentication, Authorization, Accounting) for WLANs using ClearPass Policy Manager (CPPM). It covers securing wireless networks against unauthorized access. A key skill assessed is configuring AAA protocols effectively.
- Topic 12: Secure Wired AOS-CX: This section evaluates the skills of Network Security Engineers focusing on deploying AAA for wired devices with CPPM. It includes configuring 802.1x authentication for access points. A significant skill measured is implementing AAA protocols for wired networks.
- Topic 13: Secure the WAN: This section targets WAN Engineers and covers automating VPN deployment for WAN using Aruba SD-Branch solutions. It discusses designing remote VPNs with VIA Endpoint classification. A key skill assessed is configuring secure VPN connections effectively.
- Topic 14: Threat Detection: This section measures the skills of Incident Response Analysts focusing on investigating alerts from Aruba Central and interpreting packet captures for threat detection. A critical skill measured is analyzing alerts to identify potential security incidents.
- Topic 15: Troubleshooting: This section evaluates the skills of Network Troubleshooters focusing on deploying Network Analytic Engine (NAE) scripts for monitoring network performance. It includes performing packet captures locally or via Aruba Central. A key skill assessed is troubleshooting network issues using analytics.
- Topic 16: Endpoint Classification: This section measures the skills of Endpoint Security Analysts focusing on analyzing endpoint classification data to identify risks within a network environment. It also covers analyzing data on CPDI for enhanced security insights. A significant skill measured is assessing endpoint risk levels accurately.
- Topic 17: Forensics: This section targets Forensic Analysts and explains CPDI capabilities for displaying network conversations on supported Aruba devices. It emphasizes how these capabilities aid in forensic investigations post-incident. A key skill assessed is utilizing CPDI for effective forensic analysis.
Free HP HPE7-A02 Exam Actual Questions
Note: Premium Questions for HPE7-A02 were last updated On Jun. 03, 2026 (see below)
A company has HPE Aruba Networking gateways that implement gateway IDS/IPS. Admins sometimes check the Security Dashboard, but they want a faster way to discover if a gateway starts detecting threats in traffic.
What should they do?
1. The Need for Faster Threat Notifications
Admins need immediate alerts when threats are detected by the gateway's IDS/IPS functionality. Regularly checking the Security Dashboard is inefficient, so an automated notification system is essential for faster response times.
2. Explanation of Each Option
A . Set up Webhooks that are attached to the HPE Aruba Networking Central Threat Dashboard:
Incorrect:
Webhooks are useful for integrating alerts with third-party tools or custom workflows. However, setting up email notifications through global alert settings is faster and simpler for this purpose.
B . Use Syslog to integrate the gateways with HPE Aruba Networking ClearPass Policy Manager (CPPM) event processing:
Incorrect:
Syslog integration with CPPM is typically used for logging and correlating events, not for real-time notifications about threats.
CPPM is better suited for policy enforcement, not instant threat alerts.
C . Set up email notifications using HPE Aruba Networking Central's global alert settings:
Correct:
HPE Aruba Networking Central has global alert settings that allow admins to configure email notifications for specific events, such as threat detection.
This is the simplest and most effective way to ensure admins receive immediate notifications when threats are detected by the gateways.
D . Integrate HPE Aruba Networking ClearPass Device Insight (CPDI) with Central and schedule hourly reports:
Incorrect:
While CPDI integration provides enhanced device profiling, it is not directly tied to gateway IDS/IPS threat detection.
Hourly reports are not real-time notifications and would not meet the requirement for faster threat alerts.
Final Recommendation
Setting up email notifications through HPE Aruba Networking Central's global alert settings provides the most direct and efficient solution for immediate threat detection alerts.
Reference
HPE Aruba Networking Central Alert Management Documentation.
Aruba IDS/IPS and Security Dashboard Configuration Guide.
Email Notification Setup for Aruba Central Threat Alerts.
A company is implementing HPE Aruba Networking Wireless IDS/IPS (WIDS/WIPS) on its AOS-10 APs, which are managed in HPE Aruba Networking Central.
What is one requirement for enabling detection of rogue APs?
To enable the detection of rogue APs with HPE Aruba Networking Wireless IDS/IPS (WIDS/WIPS) on AOS-10 APs managed in HPE Aruba Networking Central, each AP must have a Foundation with Security license. This license enables advanced security features, including rogue AP detection, which is crucial for maintaining a secure wireless environment and protecting against unauthorized access points.
Refer to the exhibit.
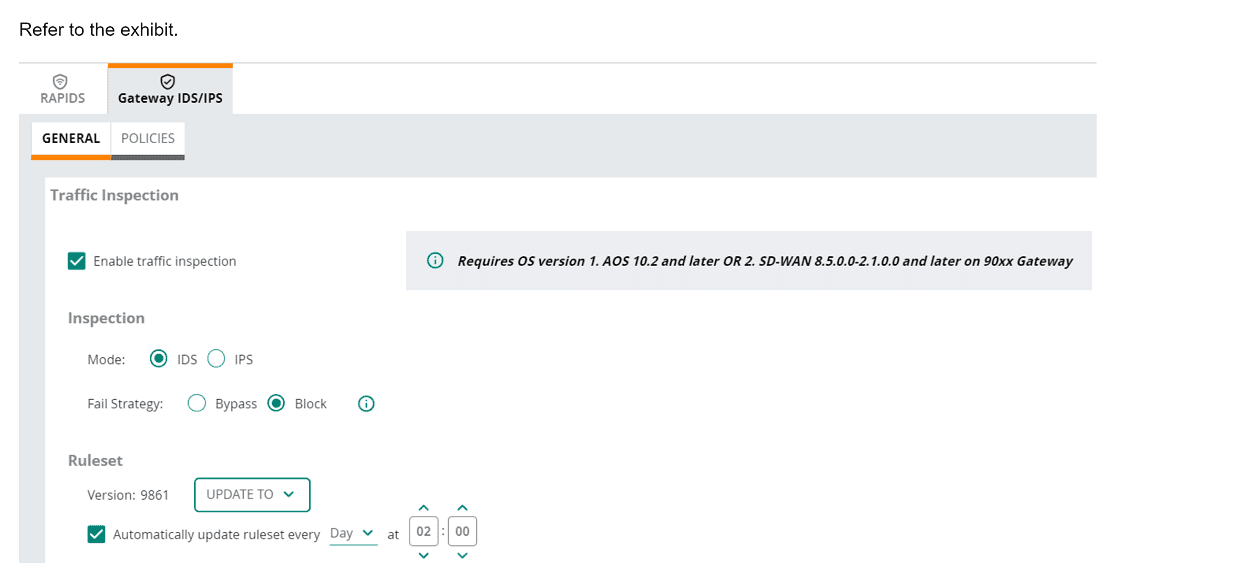
(Note that the HPE Aruba Networking Central interface shown here might look slightly different from what you see in your HPE Aruba Networking Central
interface as versions change; however, similar concepts continue to apply.)
An HPE Aruba Networking 9x00 gateway is part of an HPE Aruba Networking Central group that has the settings shown in the exhibit. What would cause the
gateway to drop traffic as part of its IDPS settings?
In the exhibit, the HPE Aruba Networking Central settings for the 9x00 gateway show that traffic inspection is enabled, and the gateway is set to operate in IDS (Intrusion Detection System) mode with the fail strategy set to 'Block'. This configuration means that the gateway will drop traffic if it matches a rule in the active ruleset.
1.Active Ruleset: The ruleset version 9861 is active, and the gateway is configured to automatically update the ruleset daily.
2.Traffic Matching Rules: When traffic matches a rule in the active ruleset, it is flagged as suspicious or malicious.
3.Block Mode: Since the fail strategy is set to 'Block', any traffic that matches a rule in the active ruleset will be dropped to prevent potential threats.
A port-access role for AOS-CX switches has this policy applied to it:
plaintext
Copy code
port-access policy mypolicy
10 class ip zoneC action drop
20 class ip zoneA action drop
100 class ip zoneB
The classes have this configuration:
plaintext
Copy code
class ip zoneC
10 match tcp 10.2.0.0/16 eq https
class ip zoneA
10 match ip any 10.1.0.0/16
class ip zoneB
10 match ip any 10.0.0.0/8
The company wants to permit clients in this role to access 10.2.12.0/24 with HTTPS. What should you do?
Comprehensive Detailed Explanation
The requirement is to permit HTTPS traffic from clients to the 10.2.12.0/24 subnet.
ZoneC is configured to drop all HTTPS traffic to the 10.2.0.0/16 subnet. Therefore, the first match in the zoneC class (priority 10) will drop the desired traffic.
To override this behavior, you must add a higher-priority rule (lower rule number) to zoneC that explicitly matches 10.2.12.0/24 and permits the traffic.
Thus, adding the rule 5 match any 10.2.12.0/24 eq https to zoneC ensures the desired traffic is permitted while maintaining the drop behavior for the rest of 10.2.0.0/16.
Reference
AOS-CX Role-Based Access Control documentation.
Understanding class priority and policy rule ordering in AOS-CX.
A company has Aruba APs that are controlled by Central and that implement WIDS. When you check WIDS events, you see a "detect valid SSID misuse" event. What can you interpret from this event, and what steps should you take?
The 'Detect Valid SSID Misuse' event in Aruba's Wireless Intrusion Detection System (WIDS) indicates that a valid SSID, associated with your network, is being broadcast from an unauthorized source. This scenario often signals a potential rogue access point attempting to deceive clients into connecting to it (e.g., for credential harvesting or man-in-the-middle attacks).
1. Explanation of Each Option
A . Clients are failing to authenticate to corporate SSIDs. You should first check for misconfigured authentication settings and then investigate a possible threat:
Incorrect:
This event is not related to authentication failures by legitimate clients.
Misconfigured authentication settings would lead to events like 'authentication failures' or 'radius issues,' not 'valid SSID misuse.'
B . Admins have likely misconfigured SSID security settings on some of the company's APs. You should have them check those settings:
Incorrect:
This event refers to an external device broadcasting your SSID, not misconfiguration on the company's authorized APs.
WIDS differentiates between valid corporate APs and rogue APs.
C . Hackers are likely trying to pose as authorized APs. You should use the detecting radio information and immediately track down the device that triggered the event:
Correct:
This is the most likely cause of the 'detect valid SSID misuse' event. A rogue AP broadcasting a corporate SSID could lure clients into connecting to it, exposing sensitive credentials or traffic.
Immediate action includes:
Using the radio information from the event logs to identify the rogue AP's location.
Physically locating and removing the rogue device.
Strengthening WIPS/WIDS policies to prevent further misuse.
D . This event might be a threat but is almost always a false positive. You should wait to see the event over several days before following up on it:
Incorrect:
While false positives are possible, 'valid SSID misuse' is a critical security event that should not be ignored.
Delaying action increases the risk of successful attacks against your network.
2. Recommended Steps to Address the Event
Review Event Logs:
Gather details about the rogue AP, such as SSID, MAC address, channel, and signal strength.
Locate the Rogue Device:
Use the detecting AP's radio information and signal strength to triangulate the rogue AP's physical location.
Respond to the Threat:
Remove or disable the rogue device.
Notify the security team for further investigation.
Prevent Future Misuse:
Strengthen security policies, such as enabling client whitelists or enhancing WIPS protection.
Reference
Aruba WIDS/WIPS Configuration and Best Practices Guide.
Aruba Central Security Event Analysis Documentation.
Wireless Threat Management Using Aruba Networks.
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Paul Jones
2 days agoAnthony Allen
18 days agoDeborah Phillips
29 days agoTiffany Bailey
1 month agoOlivia Nguyen
1 month agoMargaret Flores
1 month agoGary Garcia
1 month agoStephen Rogers
1 month agoElizabeth Mitchell
26 days agoLemuel
2 months agoGary
2 months agoParis
3 months agoColette
3 months agoUlysses
3 months agoVannessa
3 months agoStephanie
4 months agoVallie
4 months agoCarri
4 months agoCiara
4 months agoDarci
4 months agoTarra
5 months agoKiley
5 months agoCorazon
5 months agoJanella
5 months agoJackie
6 months agoAmmie
6 months agoShawnna
6 months agoRueben
6 months agoDulce
7 months agoCorinne
7 months agoTrina
7 months agoCorrie
7 months agoAmie
8 months agoJohanna
8 months agoMelita
8 months agoElliot
8 months agoTimmy
8 months agoTonette
8 months agoTerrilyn
9 months agoJulian
9 months agoRoyal
9 months agoAlonso
11 months agoLaticia
11 months agoTiera
12 months agoStephen
12 months agoOcie
1 year agoLewis
1 year agoCharlene
1 year agoBenedict
1 year agoLavonda
1 year agoDelsie
1 year agoDenny
1 year agoJose
1 year agoHarrison
1 year agoErasmo
1 year agoElza
1 year agoErick
1 year agoZoila
1 year agoCatalina
1 year ago