HashiCorp HCVA0-003 Exam Questions
- Topic 1: Authentication Methods: This section of the exam measures the skills of Security Engineers and covers authentication mechanisms in Vault. It focuses on defining authentication methods, distinguishing between human and machine authentication, and selecting the appropriate method based on use cases. Candidates will learn about identities and groups, along with hands-on experience using Vault's API, CLI, and UI for authentication. The section also includes configuring authentication methods through different interfaces to ensure secure access.
- Topic 2: Vault Policies: This section of the exam measures the skills of Cloud Security Architects and covers the role of policies in Vault. Candidates will understand the importance of policies, including defining path-based policies and capabilities that control access. The section explains how to configure and apply policies using Vault’s CLI and UI, ensuring the implementation of secure access controls that align with organizational needs.
- Topic 3: Vault Tokens: This section of the exam measures the skills of IAM Administrators and covers the types and lifecycle of Vault tokens. Candidates will learn to differentiate between service and batch tokens, understand root tokens and their limited use cases, and explore token accessors for tracking authentication sessions. The section also explains token time-to-live settings, orphaned tokens, and how to create tokens based on operational requirements.
- Topic 4: Vault Leases: This section of the exam measures the skills of DevOps Engineers and covers the lease mechanism in Vault. Candidates will understand the purpose of lease IDs, renewal strategies, and how to revoke leases effectively. This section is crucial for managing dynamic secrets efficiently, ensuring that temporary credentials are appropriately handled within secure environments.
- Topic 5: Secrets Engines: This section of the exam measures the skills of Cloud Infrastructure Engineers and covers different types of secret engines in Vault. Candidates will learn to choose an appropriate secrets engine based on the use case, differentiate between static and dynamic secrets, and explore the use of transit secrets for encryption. The section also introduces response wrapping and the importance of short-lived secrets for enhancing security. Hands-on tasks include enabling and accessing secrets engines using the CLI, API, and UI.
- Topic 6: Encryption as a Service: This section of the exam measures the skills of Cryptography Specialists and focuses on Vault’s encryption capabilities. Candidates will learn how to encrypt and decrypt secrets using the transit secrets engine, as well as perform encryption key rotation. These concepts ensure secure data transmission and storage, protecting sensitive information from unauthorized access.
- Topic 7: Vault Architecture Fundamentals: This section of the exam measures the skills of Site Reliability Engineers and provides an overview of Vault's core encryption and security mechanisms. It covers how Vault encrypts data, the sealing and unsealing process, and configuring environment variables for managing Vault deployments efficiently. Understanding these concepts is essential for maintaining a secure Vault environment.
- Topic 8: Vault Deployment Architecture: This section of the exam measures the skills of Platform Engineers and focuses on deployment strategies for Vault. Candidates will learn about self-managed and HashiCorp-managed cluster strategies, the role of storage backends, and the application of Shamir secret sharing in the unsealing process. The section also covers disaster recovery and performance replication strategies to ensure high availability and resilience in Vault deployments.
- Topic 9: Access Management Architecture: This section of the exam measures the skills of Enterprise Security Engineers and introduces key access management components in Vault. Candidates will explore the Vault Agent and its role in automating authentication, secret retrieval, and proxying access. The section also covers the Vault Secrets Operator, which helps manage secrets efficiently in cloud-native environments, ensuring streamlined access management.
Free HashiCorp HCVA0-003 Exam Actual Questions
Note: Premium Questions for HCVA0-003 were last updated On May. 25, 2026 (see below)
After encrypting data using the Transit secrets engine, you've received the following output. Which of the following is true based on the output displayed below?
Key: ciphertext Value: vault:v2:45f9zW6cglbrzCjI0yCyC6DBYtSBSxnMgUn9B5aHcGEit71xefPEmmjMbrk3
Comprehensive and Detailed in Depth
A: v2 shows the key was rotated once. Correct.
B: Transit doesn't store data. Incorrect.
C: v2 is the key version, not data version. Incorrect.
D: No transit v2 option exists. Incorrect.
Overall Explanation from Vault Docs:
''Ciphertext is prepended with the key version (e.g., v2)... Indicates rotation.''
After decrypting data using the Transit secrets engine, the plaintext output does not match the plaintext credit card number that you encrypted. Which of the following answers provides a solution?
$ vault write transit/decrypt/creditcard ciphertext="vault:v1:cZNHVx+sxdMEr......."
Key: plaintext Value: Y3JlZGl0LWNhcmQtbnVtYmVyCg==
Comprehensive and Detailed in Depth
A: Sealing would prevent decryption, not return encoded data. Incorrect.
B: Permission issues don't return encoded data. Incorrect.
C: Transit returns base64-encoded plaintext; decoding Y3JlZGl0LWNhcmQtbnVtYmVyCg== yields ''credit-card-number''. Correct.
D: No evidence of corruption; it's a format issue. Incorrect.
Overall Explanation from Vault Docs:
''All plaintext data must be base64-encoded... Decode it to reveal the original value.''
A user issues the following cURL command to encrypt data using the transit engine and the Vault AP:
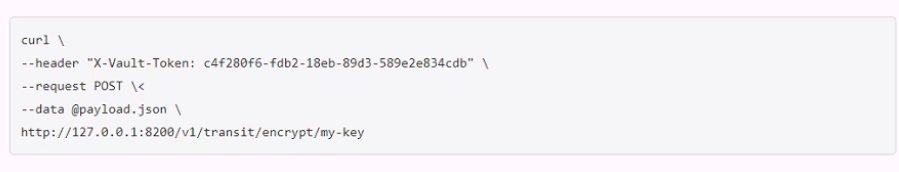
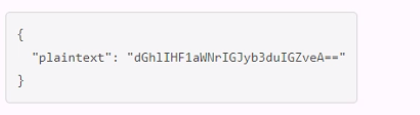
Which payload.json file has the correct contents?
A.
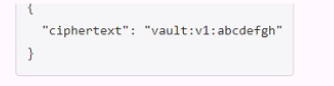
B.
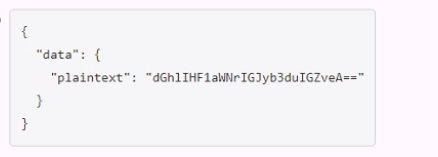
C.
D.

The payload.json file that has the correct contents is C. This file contains a JSON object with a single key, ''plaintext'', and a value that is the base64-encoded string of the data to be encrypted.This is the format that the Vault API expects for the transit encrypt endpoint1. The other files are not correct because they either have the wrong key name, the wrong value format, or the wrong JSON syntax.
Encrypt Data - Transit Secrets Engine | Vault | HashiCorp Developer
An application is trying to use a dynamic secret in which the lease has expired. What can be done in order for the application to successfully request data from Vault?
Comprehensive and Detailed in Depth
Once a dynamic secret's lease expires, it cannot be renewed or reused; a new secret must be requested. The HashiCorp Vault documentation states: 'A lease must be renewed before it has expired. Once it has expired, it is permanently revoked and a new secret must be requested.' This means that after expiration, the secret is invalidated, and the application must obtain a new secret with a new lease to regain access.
Trying an expired secret (A) is futile as it's revoked. Performing a lease renewal (B) is impossible post-expiration, as the docs note: 'Renewal must occur before the lease expires.' Extending the TTL (D) isn't an option for an expired lease. Thus, C is the correct action.
HashiCorp Vault Documentation - Leases: Lease Renew and Revoke
All Vault instances, or clusters, include two built-in policies that are created automatically. Choose the two policies below and the correct information regarding each policy. (Select two)
Comprehensive and Detailed In-Depth
Vault automatically creates two built-in policies: root and default.
A: The root policy is created at initialization, granting superuser privileges (full access to all paths and operations). It's attached to root tokens and cannot be deleted or modified, per the policies documentation.
C: The default policy is also created automatically, providing basic permissions (e.g., token management). It's attached to all non-root tokens by default, can be modified, but cannot be deleted, as stated in the docs.
B: No admin policy is automatically created; administrative policies must be defined manually.
D: The default policy can be modified, contradicting this option.
Built-in Policies
- Select Question Types you want
- Set your Desired Pass Percentage
- Allocate Time (Hours : Minutes)
- Create Multiple Practice tests with Limited Questions
- Customer Support
Brian Torres
13 days agoDeborah Cook
19 days agoDaniel Hernandez
1 month agoJoseph Wilson
29 days agoAmanda Perez
1 month agoCharles Allen
20 days agoChristopher Rogers
17 days agoAmanda Green
1 month agoCecilia
2 months agoSelma
2 months agoMary
2 months agoBilly
3 months agoTimothy
3 months agoDesmond
3 months agoHorace
3 months agoBrinda
4 months agoViola
4 months agoFiliberto
4 months agoJustine
4 months agoYoko
5 months agoNoemi
5 months agoCory
5 months agoJovita
5 months agoErinn
6 months agoFlorinda
6 months agoKathrine
6 months agoBok
6 months agoGlory
7 months agoLynna
7 months agoLawrence
7 months agoDesmond
7 months agoDewitt
8 months agoAileen
8 months agoMarlon
8 months agoShonda
8 months agoFletcher
8 months agoEloisa
8 months agoEdna
9 months agoAmos
9 months agoDominga
9 months agoEliz
11 months agoCorinne
11 months agoAlaine
11 months agoMalcolm
12 months agoAnnice
1 year agoHubert
1 year agoLizbeth
1 year agoAmie
1 year agoRolland
1 year agoKristeen
1 year agoDella
1 year ago