GIAC GCED Exam - Topic 8 Question 20 Discussion
Topic #: 8
Although the packet listed below contained malware, it freely passed through a layer 3 switch. Why didn't the switch detect the malware in this packet?
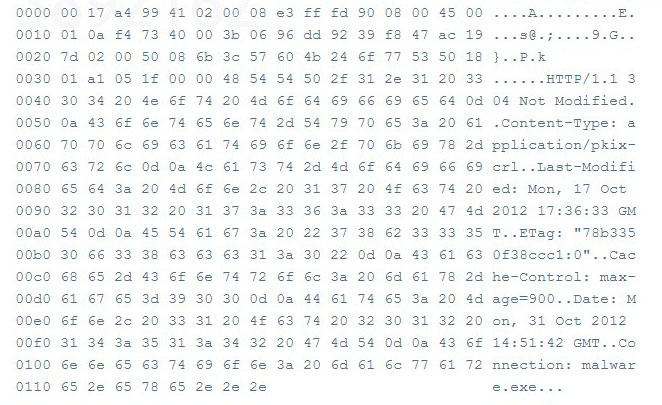
Routers, layer 3 switches, some firewalls, and other gateways are packet filtering devices that use access control lists (ACLs) and perform packet inspection. This type of device uses a small subset of the packet to make filtering decisions, such as source and destination IP address and protocol. These devices will then allow or deny protocols based on their associated ports. This type of packet inspection and access control is still highly susceptible to malicious attacks, because payloads and other areas of the packet are not being inspected. For example, application level attacks that are tunneled over open ports such as HTTP (port 80) and HTTPS (port 443).
Jenifer
6 months agoDion
6 months agoRusty
6 months agoTarra
6 months agoAndra
6 months agoBarrie
7 months agoRuthann
7 months agoDaisy
7 months agoHubert
7 months agoLillian
7 months agoTish
7 months agoLeslie
7 months ago