Free Eccouncil 312-50 Exam Dumps June 2026
Here you can find all the free questions related with Eccouncil Certified Ethical Hacker v13 (312-50) exam. You can also find on this page links to recently updated premium files with which you can practice for actual Eccouncil Certified Ethical Hacker v13 Exam. These premium versions are provided as 312-50 exam practice tests, both as desktop software and browser based application, you can use whatever suits your style. Feel free to try the Certified Ethical Hacker v13 Exam premium files for free, Good luck with your Eccouncil Certified Ethical Hacker v13 Exam.MultipleChoice
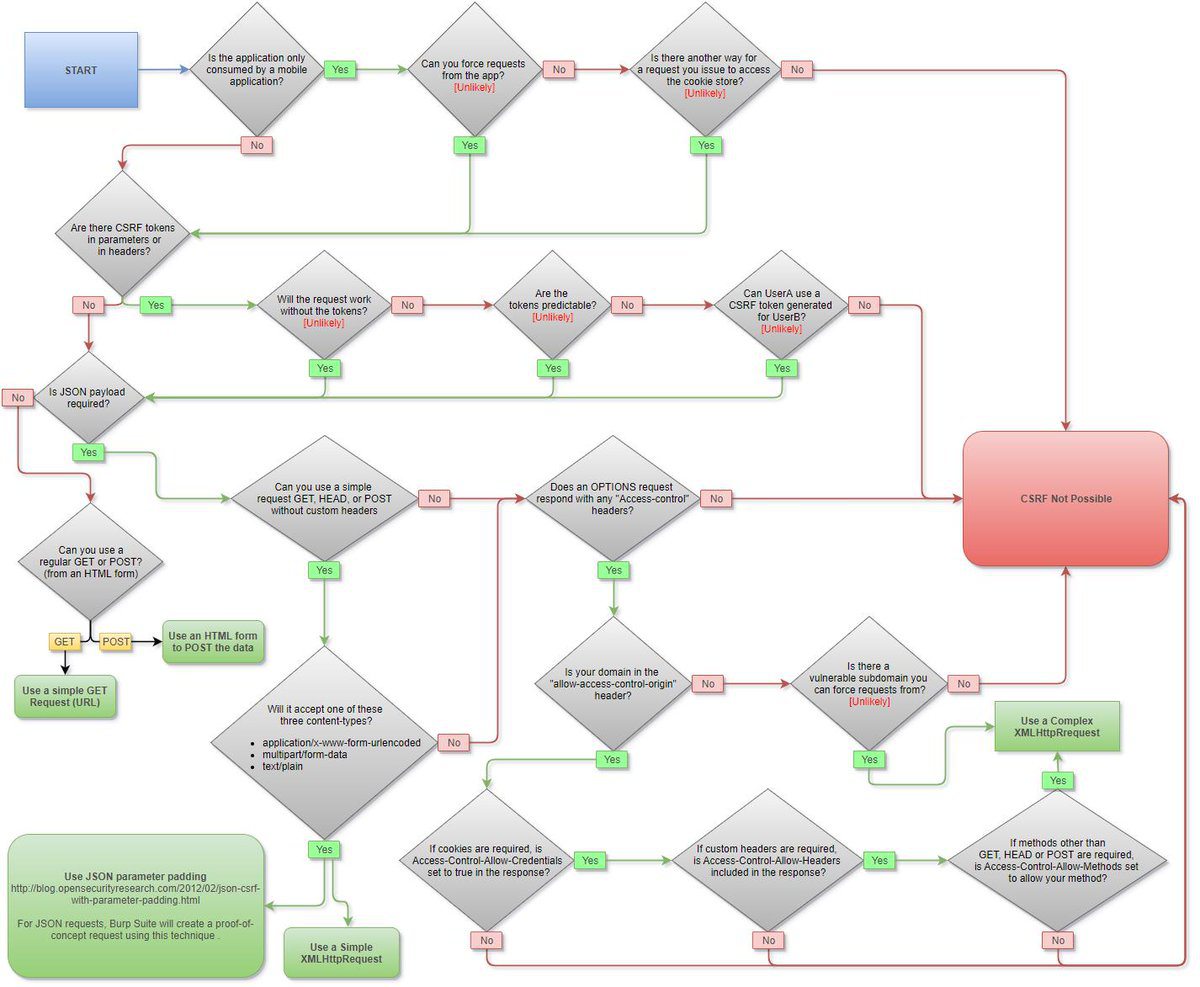
An attacker changes the profile information of a particular user (victim) on the target website. The attacker uses this string to update the victim's profile to a text file and then submit the data to the attacker's database.
< iframe src=''''http://www.vulnweb.com/updateif.php'''' style=''''display:none'''' > < /iframe >
What is this type of attack (that can use either HTTP GET or HTTP POST) called?
OptionsMultipleChoice
You are the chief security officer at AlphaTech, a tech company that specializes in data storage solutions. Your company is developing a new cloud storage platform where users can store their personal files. To ensure data security, the development team is proposing to use symmetric encryption for data at rest. However, they are unsure of how to securely manage and distribute the symmetric keys to users. Which of the following strategies
would you recommend to them?
OptionsMultipleChoice
John is an incident handler at a financial institution. His steps in a recent incident are not up to the standards of the company. John frequently forgets some steps and procedures while handling responses as they are very stressful to perform. Which option best actions should John take to overcome this problem with the least administrative effort?
OptionsMultipleChoice
What does the --oX flag do in an Nmap scan?
OptionsMultipleChoice
Which of the below hashing functions are not recommended for use?
OptionsMultipleChoice
Which of the following is the best countermeasure to encrypting ransomwares?
OptionsMultipleChoice
If an attacker uses the command SELECT*FROM user WHERE name = 'x' AND userid IS NULL; --'; which type of SQL injection attack is the attacker performing?
OptionsMultipleChoice
You are working as a Security Analyst in a company XYZ that owns the whole subnet range of 23.0.0.0/8 and 192.168.0.0/8.
While monitoring the data, you find a high number of outbound connections. You see that IP's owned by XYZ (Internal) and private IP's are communicating to a Single Public IP. Therefore, the Internal IP's are sending data to the Public IP.
After further analysis, you find out that this Public IP is a blacklisted IP, and the internal communicating devices are compromised.
What kind of attack does the above scenario depict?
OptionsMultipleChoice
Trinity needs to scan all hosts on a /16 network for TCP port 445 only. What is the fastest way she can accomplish this with Nmap? Stealth is not a concern.
OptionsMultipleChoice
Darius is analysing IDS logs. During the investigation, he noticed that there was nothing suspicious found and an alert was triggered on normal web application traffic. He can mark this alert as:
Options