Deal of The Day! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
CompTIA Exam SY0-601 Topic 3 Question 24 Discussion
Actual exam question for
CompTIA's
SY0-601 exam
Question #: 24
Topic #: 3
[All SY0-601 Questions]
Topic #: 3
A security analyst is investigating an incident to determine what an attacker was able to do on a compromised laptop. The analyst reviews the following SIEM log:
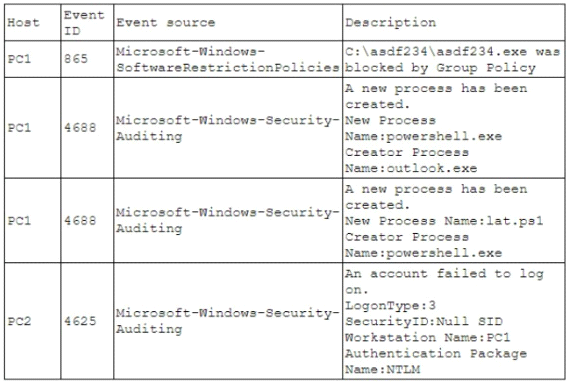
Which of the following describes the method that was used to compromise the laptop?
Suggested Answer:
A
Currently there are no comments in this discussion, be the first to comment!